Consider i have a phone, and it’s bootloader is unlocked. What is the worst that could happen?
I’m interested in the security aspect of it. Consider you’re detained by the police, and they want access to your phone. Can they get access if the bootloader is unlocked?
What is the role of the password? I.e., i’m using a 4-digit PIN for my phone today. Can the phone’s data be secured against police force if they get physical access to the phone?
To further elaborate:
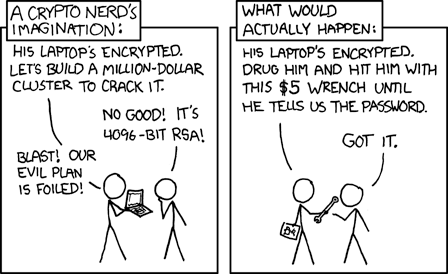
I’m well aware of the XKCD:
I’m wondering, apart from applying physical force, what are the surveillance aspects? Could somebody sneakily install spyware on my phone that can read all files on the phone’s internal storage if they get a physical hold of it for (let’s say) 15 minutes?
While unlocking the bootloader […] unleashes the full potential of the bootloader, it also poses a security risk. Even with your lockscreen protected with a pattern/PIN/password, not having flashed a custom recovery, having an anti-theft app installed (maybe even converted/installed as a system app) your phone’s data is easily accessible for a knowledgeable thief.
All the thief needs to do is reboot into the bootloader and boot or flash a custom recovery such as ClockWorkMod or TWRP. It’s then possible to boot into recovery and use ADB commands to gain access to the phone’s data on the internal memory (unless you have it encrypted) and copy/remove files at will.
Granted, the risk seems low. The thief would not only require knowledge of fastboot, he would have to turn off the phone before you have issued a wipe command using an anti-theft app. You could of course flash back the stock recovery & relock the bootloader after being done with flashing stuff, but that would require you to unlock it again if needed which will erase your userdata.
Of course, a thief can/is also the government.
But, most phones can be unlocked by the pigs regardless, with eg. Cellebrite. The best bet is probably a pixel, as it can be relocked easily, with graphene. Or no phone at all.
Also, I’d guess many Cellebrite tricks work with (weak?) pins/patterns. Use a password, and no fingerprint. And on eg. graphene, the emergency wipe after 10 wrong pws etc.Thank you for your comment.
I assume using a password is better than using a PIN/pattern (as you said) because it has more entropy.
IIRC Android actually encrypts all userdata by default nowadays but it only encrypts userdata and not the system partition.
So if an attacker got access to the phone, they could install an update on the system partition that includes spyware and then spy on my password next time that i enter it. So once an attacker got a hold of my phone, i should assume they installed spyware on the system partition and the phone is no longer trustworthy. In that case, i’d have to flash and reformat the whole phone.
(If i re-lock the bootloader, it has the advantage that i’d be notified if an attacker wrote updates to the system partition because all userdata would be wiped.)
(If i re-lock the bootloader, it has the advantage that i’d be notified if an attacker wrote updates to the system partition because all userdata would be wiped.)
are you sure that makes the data wiped? as I know, locking itself wipes, but it is not possible to write partitions anymore with standard tools, and the bootloader will check signatures with dm-verity (a linux tool) and if it doesn’t match it’ll just refuse to boot
In that case, i’d have to flash and reformat the whole phone.
you could try restoring partition images. needs testing though, maybe it doesn’t work for some reason
consequences of an unlocked bootloader
The Transport of London app refuses to start on your device (as well as several other apps from overly hypocritical idiots).
Someone who stole it can flash their own modified OS. And dump the phone’s data, probably in an encrypted state.
No banking apps
deleted by creator
Yes but no. Physical access sure. Software access, probably not. Also more depends more on the os than the firmware.
Someone can easily extract all of your data off the phone/install malware.
With prolonged physical access, and a particular definition of “easily”.
If the bootloader is unlocked then very easy. Just boot a custom recovery and backup the internal storage to your pc. Nobody’s going to try to extract the entirety of your phones storage while you’re taking a piss.
that’s not how it works at least for half a decade now. unless a manufacturer has gone way out of their way to disable it, android phones need to support some kind of data encryption to be certified by google
yeah Android actually encrypts all userdata by default nowadays
the PIN/pattern/password is used as the encryption/decryption key. That’s why i guess choosing a 4-letter PIN as lock protection is weak and could be broken.
It would be nice if you could use a password for encryption (that means you’d have to enter it once after every re-boot), and then use a PIN while the device is running. Sadly i haven’t found a way to do that yet.
It would be nice if you could use a password for encryption (that means you’d have to enter it once after every re-boot), and then use a PIN while the device is running. Sadly i haven’t found a way to do that yet.
also if we could set up multiple authentication methods, such that both biometric and pin is required. it would help against shoulder- and camera surfing, and legally against forcing your hand to the sensor to get it unlocked.
I never said it wouldn’t be encrypted. But if they extract it and they’re willing (or there’s an exploit) they could de encrypt it.
Or it could be like the Android 7(?) days where you flash a quick zip and your data is unencrypted.



